Posted inCybersecurity News
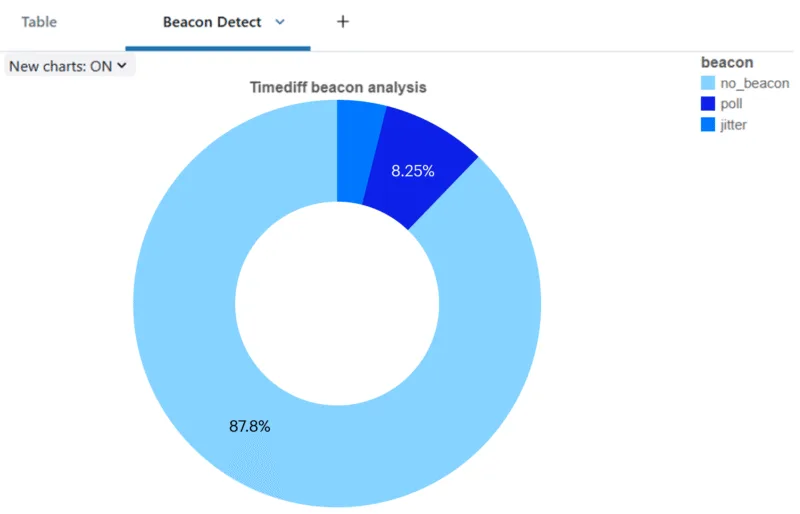
New Jitter-Trap tool helps organizations detect stealthy beacon traffic used by C2 communications in victim networks.
The new Jitter-Trap tool from Varonis is designed to help organizations detect stealthy beacon traffic used by attackers to establish and maintain command and control (C2) communication within victim networks. Beacons are commonly employed by threat actors—including state-sponsored groups and cybercriminals—to avoid detection while executing post-exploitation activities such as data exfiltration, lateral movement, and persistent access.